Working on your VMware environment, we often needed remote access to your ESXi hosts. Accessing the ESXi Host via SSH offers administrators the ability to maintain, troubleshoot, and remediate issues by using a Secure Shell client such as PuTTY. As per the security concern, SSH is disabled by default. However, you can enable it for remote command execution in multiple ways. In this post, we will provide you a walk through the different processes of enabling SSH on VMware ESXi 6.5 hosts.
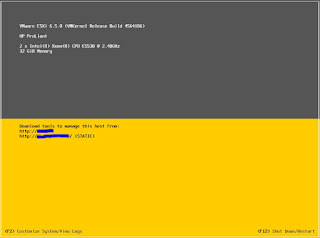
Enable via Direct Console User Interface (DCUI)
Login in ESXi Direct Console User Interface (DCUI) and Press F2 Key.
It will ask you for root credentials.
Now go to System Customization screen and select Troubleshooting Options.
Under Troubleshooting, go to Mode Option and choose Enable SSH.
SSH will show now Enabled.
Press Esc to go back to main menu.
Enable via vSphere Web Client (Host)
Log into the ESXi via the Web Client. It must be https://localhostname/UI. Log in with root credentials.
From the Home page select Host and go to Action. In Action gear select Services and choose Enable Secure Shell.
Or you can choose another method to enable the SSH.
Go to Manage and navigate to Services Tab. Find the SSH service from the list and Start it via Action gear.
Enable via vSphere Web Client (V-Center)
Log into vCenter via Web Client. It must be https://vcenterhostname/UI. Log in with root credentials.
Search and select the host, and Navigate to Configure Tab and scroll down to System section and select Security Profile.
Scroll down to Service and click Edit.
Locate SSH Service and Start.






Comments
Post a Comment